CyberArk Defender + Sentry Exam Braindumps
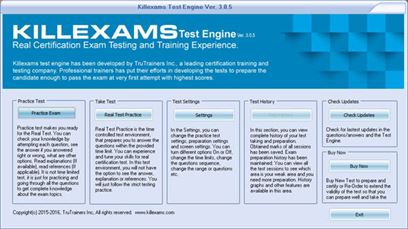
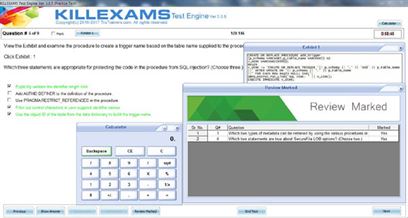
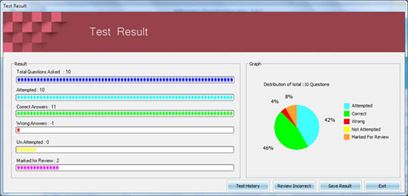
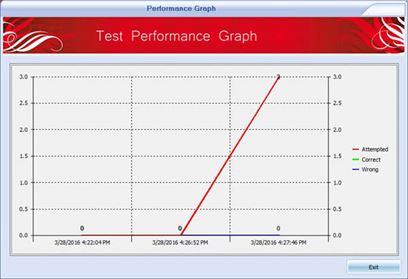
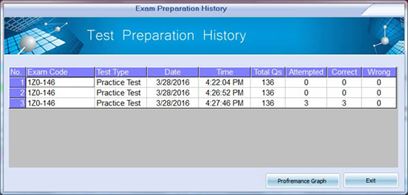
Killexams.com CAU302 Exam Braindumps contain complete question pool, updated in April 2024 including VCE exam simulator that will help you get high marks in the exam. All these CAU302 exam questions are verified by killexams certified professionals and backed by 100% money back guarantee.
CAU302 pdf - CyberArk Defender + Sentry Updated: 2024 | ||||||||
| Killexams CAU302 practice questions with Real Questions | ||||||||
 |
||||||||
|
||||||||
|
Exam Code: CAU302 CyberArk Defender + Sentry pdf January 2024 by Killexams.com team | ||||||||
CAU302 CyberArk Defender + Sentry This certification provides the practical knowledge and technical skills to maintain day-to-day operations and support the on-going performance of the CyberArk Privileged Access Security Solution The CyberArk Defender Certification tests for the practical knowledge and technical skills to maintain day-to-day operations and to support the on-going maintenance of the CyberArk Privileged Account Security Solution. It is intended to certify an examinees competence to fill one of the following roles within a Privileged Account Security Program. Exam : CAU302 Exam Name : CyberArk Defender + Sentry Questions : 65 Type : multiple-choice questions Duration : 90 minutes Passing score : 70% A CyberArk Certified Defender is capable of performing the following tasks: Describing the system architecture and workflows. Successfully managing passwords (Verification, Change, and Reconciliation). Onboarding accounts using Accounts Discovery and the Password Upload Utility. Configuring sessions to be directed through a PSM. Monitoring recorded sessions. Describing how connections through a PSMP can be established. Modifying Master Policy settings. Producing reports on various system and user activities. Monitoring the CyberArk implementation. Describing and configuring the various logs that are available to troubleshoot problems. Utilizing the knowledge base and other available resources to resolve problems. Performing common administrative tasks. The CyberArk Defender Certification tests examanees ability to form the following tasks in seven knowledge domains. Only functions of the Core PAS Solution are included. Account Onboarding • Perform a bulk upload of accounts using Password Upload Utility or REST • Create an Onboarding Rule • Onboard an account from the pending accounts list • Setup a Unix Discovery • Setup a Windows Discovery • Manually onboard an account • Onboard SSH Keys with Account Uploader Application Management • Describe tools that could be used to monitor CyberArk Application Health • Use PrivateArk with Proficiency • Describe how each component communicates with others or devices on network at a high level • Maintain an appropriate chain of custody for Encryption Keys Ongoing Maintenance • Restore DR to normal operation after a failover • Backup Vault Data with PAReplicate • Resync a credential file by running createcredfile manually on the command line • Identify the log files for each component • Identify and locate component configuration files • Assemble necessary log files for submission to a case (X-RAY) • Ensure each component is operational • Open a support case with appropriate description and severity • Create or Upvote an ER • Restore an object to the vault from a PAReplicate Backup Password Management Configuration • Configure a request/approval process • Configure workflow processes to ensure non-repudiation • Setup automatic verification, management, and reconciliation of passwords or SSH Keys • Explain the differences between a logon versus a reconcile account • Configure a logon account • Configure a reconcile account • Properly configure the “SearchForUsages” Platform parameter • Configure workflow processes to reduce the risk of credential theft • Configure workflow processes to comply with audit/regulatory policies • Import a Custom Platform from the Marketplace • Duplicate a Platform • Manage the password of a supported usage • Provision a Safe • Follow a safe naming convention • Configure Safe Retention • Configure Management of Workstation Passwords using Loosely Connected Devices • Add a User/Group to a safe in accordance with access control policies • Use an OOB Platform to manage a device Security and Audit • Configure a Response to Unmanaged Credentials • Describe the various PTA detections • Configure Automatic Session Termination • Configure a Response to Credential Theft • Search for a recording • Utilize safe permissions to limit the scope of reports for specific users • Understand the purpose of EVD • Grant appropriate permission to allow users to run reports • Describe all reports and what information they give a user • Review a recording • Configure email alerts in PTA Session Management Configuration • Configure the Master Policy to enable the PSM • Grant Access to view recordings • Configure a recording safe • Make a PSM for SSH Connection using an SSH Client • Make a PSM Connection using the Connect Button • Make a PSM Connection using an RDP Client • Setup text based or video based recordings on PSM • Configure the PSM to utilize the HTML5 Gateway • Configure the Master Policy to enable the connect button • Configure the Master Policy to create PSM recordings • Configure a split workflow • Describe connection components and what they do User Management Configuration • Be able to describe the difference between safe and vault level permissions without the GUI (web or PA client) • Add an LDAP User/Group to a Local Group • Configure additional LDAP hosts • Validate Proper Function of Pre-Configured Directory Mappings • Verify an LDAP Configuration is using SSL • Add a User to a Vault Group • Configure Safe Level Permissions on a User or Group • Configure Vault Level Permissions on a User • Describe the purpose of each Built-In Vault User • Login as the Master user • Provision an internally authenticated user in the vault • Set/Reset a Vault Users Password | ||||||||
| CyberArk Defender + Sentry CyberArk CyberArk pdf | ||||||||
Other CyberArk examsCAU302 CyberArk Defender + SentryCAU201 CyberArk Defender PAM-DEF CyberArk Defender PAM-DEF-SEN CyberArk Defender PAM & Sentry CAU305 CyberArk CDE Recertification CyberArk-EPM CyberArk Endpoint Privilege Manager (EPM) solution expert PAM-CDE-RECERT CyberArk CDE Recertification (PAM-CDE-RECERT) | ||||||||
| We are doing great struggle to provide you genuine CAU302 dumps and practice test. Each CAU302 question on killexams.com has been Verified and updated by our team. All the online CAU302 dumps are tested, validated and updated according to the CAU302 course. | ||||||||
| CAU302 Dumps CAU302 Braindumps CAU302 Real Questions CAU302 Practice Test CAU302 dumps free CyberArk CAU302 CyberArk Defender + Sentry http://killexams.com/pass4sure/exam-detail/CAU302 Question: 169 It is impossible to override Mater Policy settings for a Platform A . TRUE B . FALSE Answer: B Question: 170 The vault server uses a modified version of the Microsoft Windows firewall. A . TRUE B . FALSE Answer: B Question: 171 The DR module allows an integration with Enterprise Backup software. A . TRUE B . FALSE Answer: B Question: 172 It is possible to leverage DNA to provide discovery functions that are not available with auto-detection. A . TRUE B . FALSE Answer: A Question: 173 It is possible to restrict the time of day, or day of week that a verify process can occur A . TRUE B . FALSE Answer: B Question: 174 The vault does not support Role Based Access Control A . TRUE B . FALSE Answer: B Question: 175 The Remote Desktop Services role must be properly licensed by Microsoft. A . TRUE B . FALSE Answer: A Question: 176 PSM captures a record of each command that was issued in SQL Plus. A . TRUE B . FALSE Answer: A Question: 177 What is the purpose of the Allowed Safes parameter in a CPM policy? Select all that apply. A . To Strengthen performance by reducing CPM workload. B . To prevent accidental use of a policy in the wrong safe. C . To allow users to access only the passwords they should be able to access. D . To enforce Least Privilege in CyberArk. Answer: CD Question: 178 The vault supports a number of dual factor authentication methods. A . TRUE B . FALSE Answer: B Question: 179 Multiple PVWA servers are always all active. A . TRUE B . FALSE Answer: A Question: 180 You have associated a logon account to one of your UNIX root accounts in the vault. When attempting to verify the root account�s password the CPM will� A . Ignore the logon account and attempt to log in as root. B . Prompt the end user with a dialog box asking for the login account to use. C . Log in first with the logon account, then run the su command to log in as root using the password in the vault. D . None of these. Answer: B For More exams visit https://killexams.com/vendors-exam-list Kill your exam at First Attempt....Guaranteed! | ||||||||
 Jacob Wackerhausen An Ark Full of SecurityCyberArk Software Ltd. (NASDAQ:CYBR) of Israel has been on our acquisition list for 7 years. Like Noah's ark secured the human race, CyberArk wants to make us all safer. Our Seeking Alpha article about the identity security company appeared on S A on November 28, 2018; the share price was on the move up topping $68.35 each at the time of publication. The share price closed the second week of December ’23 near its 52-week high at $204.53 then slipped to $201.25 to close the second week of December '23. In our opinion, current measures substantiate the stock’s Buy-rating status we, S A, and Wall Street analysts assign it at this time. 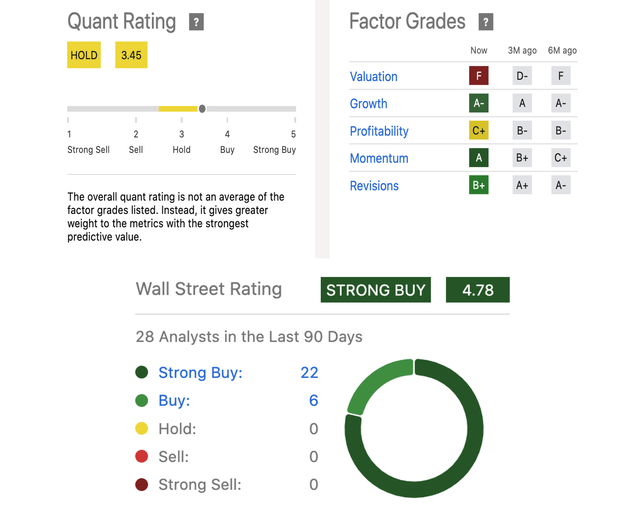
Analysts' & Quant Ratings, Factor Grades (Seeking Alpha) CyberArk stands out from its peers in several ways meaningful to investors. My associate, Dan Goldmeier, now VP of Sales & Marketing at start-up Hospice Tools in Chicago, worked with CyberArk in a former position at an Israeli software company. He rates CyberArk "a great company with some of the best tech for cybersecurity for governments and banks and enterprise companies. And the service to customers with boots on the ground is stellar." In a survey by Gartner Peer Insights, CyberArk reviews rate it higher than Microsoft (MSFT) and 22 other well-known players in the field of Identity Security. CyberArk is "better at service and support, easier to integrate and deploy, and better evaluation and contracting." A second reason for our gleam comes from the company's strategy of generating growing recurring revenue; that translates to good earnings and high margins. The quarterly gross profit margin over the last 3 quarters averages ~80% and 81.59% over all the years. That number is better than 85% of GPM of companies in the industry. CyberArk's operating and net margins rank lower than those of industry competitors but CyberArk is producing enough cash flow for the company liquidity ranking to place it mid-level among its peers. ProfileAccording to Stockanalysis.com, CyberArk is the seventh largest, Israel-based, publicly traded, business on a U. S. exchange by market cap (~$8.39B) with annual revenue touching $700M. 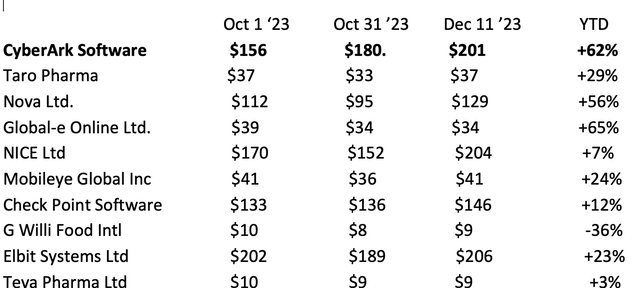
Israel-based Stocks (Goldmeier Family LLC) A primary reason for the resiliency of Israel's stocks is that most of the above companies have R&D and marketing offices overseas and customers are worldwide. Overseas locations operationally support CyberArk's Israel and West Bank locations. Its operations, productivity, and output are minimally affected by the war. 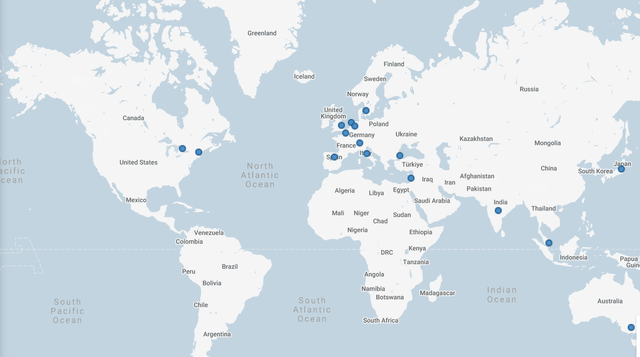
CyberArk Worldwide Locations (CyberArk) CyberArk Software develops, markets, and sells software security programs and services. It is building subscription revenue, too. Brand names include
Customers include financial services, manufacturing, insurance, healthcare, energy and utilities, transportation, retail, technology, and telecommunications industries. Private customers and government agencies are reached through CyberArk’s direct sales force, channel sales, security service providers, and advisory partners. The company was founded in 1999 when Israel’s burgeoning tech industry engendered its tag name, the Start-Up Nation. Late this year, CyberArk was named an Overall Leader in the KuppingerCole Analysts AG 2023 “Leadership Compass: Access Management” report. “The company’s overall leadership position is based on the strength of its CyberArk Identity offering across the report’s product, innovation and market categories.” CyberArk’s growth is partly attributable to its acquisition of 7 companies in software and IT at a cost of nearly $145M over the years. S A reports investment firm Wedbush Securities recently cited CyberArk among the global leaders likely to benefit from increased Washington spending next year on security and risk management; it projects total spending of $215B in ’24 or +14% Y/Y. Israel’s cybersecurity firms and government are projected to report revenue to grow in 2024 at an annual CAGR average of 11.66% hitting a market volume of $1.5B by FY ’28. This might be an underestimation considering how significantly cybersecurity firms are aiding in Israel’s anti-terror war effort. More Good NewsQ3 ’23 reported in November was one of the company’s best quarters. Demand for Identity Security is a global priority according to the CEO: “Total bookings growth accelerated and…significantly outpaced our guidance framework.” The engagement of customers on a subscription model resulted in “a break-out in terms of product ARR (annual recurring revenue) subscription growth, rising to a quarterly level," according to S A analyst Bert Hochfeld. The shareholders were also told
We foresee significant revenue growth, and better and more consistent EPS upside over the next 2 years and into the future. Identity cybersecurity is an important part of risk management in public space security, as we discussed in a accurate article about Evolv Technologies Holdings, Inc. (EVLV). We think the increase in demand for CyberArk’s products and services on a subscription basis is going to positively affect the consensus FY ‘24 EPS forecast loss to between -$1.73-to -$2.38 from the 2023 consensus between -$2.31-to -$2.40 per share. Wells Fargo (WFC) recently upgraded its average target price from $201 to $231. We see an opportunity for an average target share price of +$250 over the next 3 to 6 months with no impediments to ending this rally anytime soon. 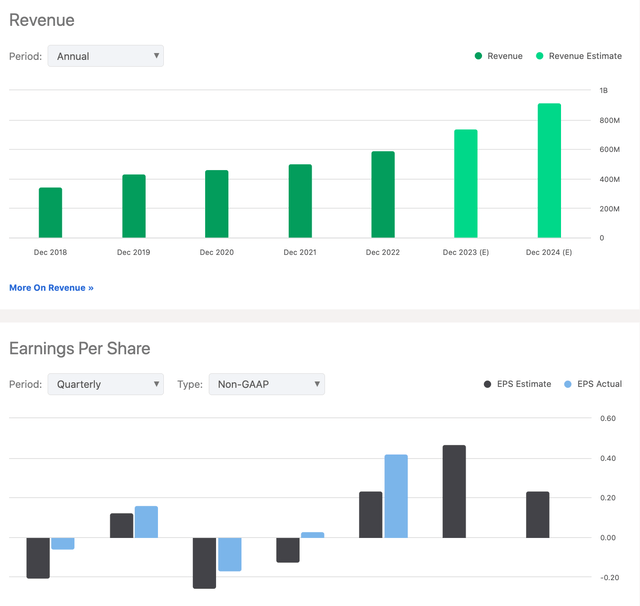
Revenue & Earnings (Seeking Alpha) Finally, media coverage and sentiment about CyberArk was bullish most of the year and seems to remain so. RisksIn our 2018 article, we wrote, “CyberArk is a solid investment for small investors interested in the cybersecurity industry. There is plenty of room for growth and opportunities for climbing to the target prices set by institutional investors.” Little has changed except, to note, that S A downgraded its Quant Rating assessment this year to Hold, as the share price soared $100 from the end of 2022 lowering its valuation. We consider this new status a risk flag and investors need to watch valuation. Another concern is the conflict in Gaza; when Israel was invaded by Hamas in October, the average share price of Israel-based firms dived around 14% to 16%. Shares of CyberArk sold for $171 each in Sep ’23, slipped to ~$156 in late October, but are back-up, as we predicted the share prices would be once initial economic-impact revisions were evaluated. Third, corporate insiders do not own many shares and that is never reassuring to retail value investors. Hedge funds consistently bought the stock in the first quarter of 2023 and in greater quantities beginning in May ’23. Since the rally, funds have tended to sell, decreasing their holdings by 102K shares last quarter. At its peak number in Q1 ’23, 33 hedge funds owned shares, 27 in Q2, and 30 at the end of Q3 ’23. We do not see any downward trend evolving yet despite the greatest risk which is the high valuation. The company holds $571.6M in debt but last reported $906.2M in cash and equivalents; plus, its market cap tops $8B. CyberArk’s net cash flow from operations is slightly up but so are liabilities. It is liquid enough to cover outstanding financial obligations. Short interest moved up to +5% on the share price rise with days to cover 3-to-4 down from +7 last August. 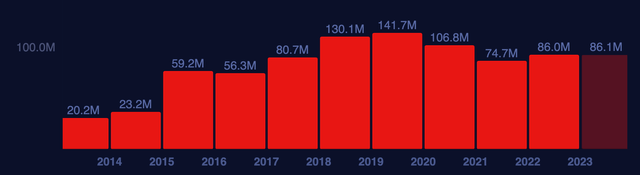
Operating Cash Flow (Macroaxis.com) CyberArk is in a labor-intensive business competing for trained innovative-thinking employees. In February ’23, the company hired another 150 employees to keep R&D apace. Officials also announced the CEO of 18 years is stepping down, but we expect any new moves to be delayed until after the war on terrorists is settled. ValuationRegarding S A’s valuation F grade, a peek at the metrics reveals the share price rally puts them out-of-sync with sector mean numbers. For example, P/E non-GAAP forward is 261.6 versus the sector mean of 23.8; PEG non-GAAP is 11.89 versus 2.03; and EV to Sales TTM and FWD is around 11 to the sector’s mean of 2.88 and 2.81, respectively. EV/EBITDA gets an F standing at 1.88 to 15.3. CyberArk’s price to various metrics all rate a D- or F. Concomitantly, its Enterprise Value has steadily risen: 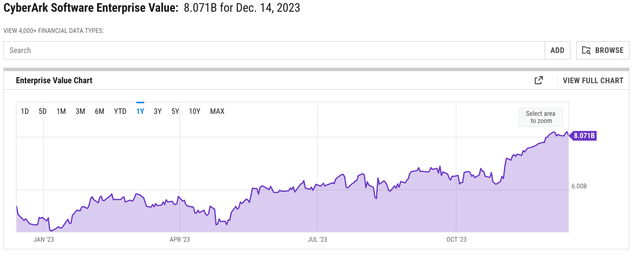 Enterprise Value Over Years (YCharts.com) In our opinion, considering EV growth, past and potential revenue and earnings growth, liquidity, potential for generating recurring income, and other metrics, we conclude the shares selling at around $210 each is a reasonable fair value but other valuation gauges suggest there is potential for the share price to move up higher. Granted, the current share price is on the expensive side of fair value; we think fair value will rise when its price-to-sales ratio becomes more balanced as the company grows, cuts debt, enjoys the results of lower loan interest rates, and Identity Security software grows in sophistication and effectiveness pushing massive industry growth. More value lies in the potential for this Israeli tech company garnering M&A attention from a suitor. These deals are at a 9 year low because of the war but identity tech companies have learned a lot from the war making CyberArk potentially more valuable. Takeaway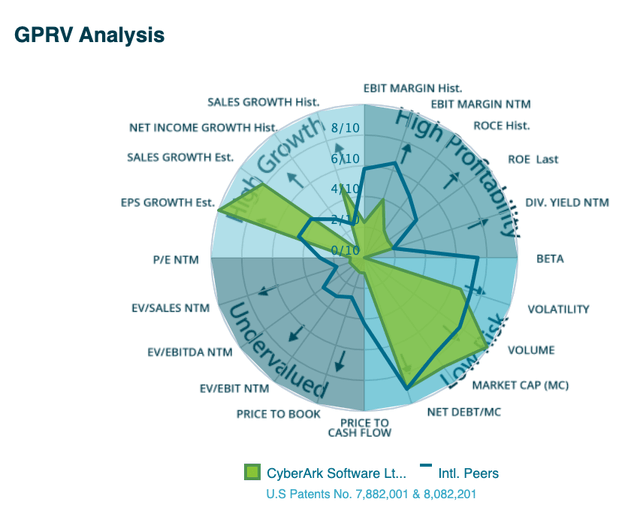
Growth & Risk Assessment (Infrontanalytics.com) We see from the valuation metrics a rising risk from sell-offs to take profits as we near the end of the year and start a new one. But predictions are, for the most part, 2024 will be a big up year for the stock market. The demand for identity security is only going to increase. We do not see any other significant downward pressures over the next 6 months on the stock. CyberArk is facing few risks, is carrying through on its subscription strategy, and has the potential for tremendous growth worldwide. It is why the company gets a better Factor Grade for Momentum from 6 and 3 months earlier and we see the stock as a Buy opportunity even at +$200 per share. Many artificial intelligence (AI) stocks have skyrocketed over the past year as the bulls worked to take advantage of the growth potential of generative AI platforms. That buying frenzy seen in the markets this year might be inflating many of those AI stocks to bubbly valuations. For those who were late to hop aboard the AI bandwagon, there are still pockets of growth elsewhere across the tech sector for shrewd investors to tap into. The cybersecurity market is one of those pockets, and stocks like CyberArk Software (CYBR 1.34%), Zscaler (ZS 0.39%), and SentinelOne (S -0.67%) also have real potential to make you a lot richer. Let's take a look at these three stocks and why they could make you forget about AI. 
Image source: Getty Images. 1. CyberArkMany cybersecurity companies protect an organization's infrastructure from external threats. But CyberArk develops tools for privileged access management (PAM) for countering internal threats like disgruntled employees and corporate spies. When it detects a network breach, it locks down the affected systems and locates the threat. CyberArk now serves over 8,000 customers worldwide, including more than 55% of the Fortune 500 and 35% of the Global 2000. Its revenue had a compound annual growth rate (CAGR) of 18% from 2017 to 2022, and analysts expect it to continue at a CAGR of 24% from 2022 to 2025. According to Markets and Markets, the global PAM market could still see a CAGR of 21.5% from 2023 to 2028. CyberArk turned unprofitable last year as it expanded its cloud-based subscription services to pivot away from single-use licenses. However, analysts expect its annual adjusted earnings before interest, taxes, depreciation, and amortization (EBITDA) to turn positive again in 2023 and more than quadruple by 2025. CyberArk's stock price has already rallied more than 50% this year and doesn't seem like a bargain at 9 times next year's sales. Nevertheless, its early mover's advantage in the PAM market and its long-term growth potential justify that higher valuation. 2. ZscalerZscaler is another company that focuses on internal threats instead of external ones. It specializes in "zero trust" tools, which treat everyone (including a company's CEO) as a potential threat to fend off intruders. But unlike other companies that install their services in on-site equipment, Zscaler only provides cloud-native services, which are stickier, easier to scale up, and don't take up any physical space. The company's revenue had a CAGR of 53% from fiscal 2018 to fiscal 2023 (which ended this July). It currently serves over 7,500 customers worldwide, including 30% of the Global 2000. But it could still have plenty of room to grow: Mordor Intelligence expects the zero-trust market to see a CAGR of 17% from 2023 to 2028. Zscaler's growth has cooled off over the past year as the macro headwinds made it tougher to gain new customers. However, analysts still expect its revenue to rise at a CAGR of 26% from fiscal 2023 to fiscal 2026 -- which implies its cloud-native advantage will enable it to grow faster than the broader zero-trust market. Zscaler's stock has rallied nearly 80% this year, and it doesn't seem cheap at 13 times this year's sales. Yet this high-growth cybersecurity company could still have plenty of room to run as more organizations tighten their digital defenses. 3. SentinelOneLastly, SentinelOne might be attractive to speculative investors who can stomach a lot of near-term volatility. It went public only two and a half years ago, but it aims to disrupt the cybersecurity sector by replacing all human analysts with AI algorithms on its Singularity platform. It claims that the approach is faster and more accurate than human-driven platforms. SentinelOne has grown like a weed since its initial public offering (IPO): Its revenue more than doubled in each of its past three fiscal years, and it expects 46% growth in fiscal 2024 (which ends in January 2024). Analysts expect its revenue to continue rising at a CAGR of 31% from fiscal 2024 to fiscal 2026. Those growth rates are incredible, but SentinelOne stock remains about 30% below its IPO price and doesn't seem too expensive at 10 times this year's sales. However, its losses are widening, and bigger competitors like CrowdStrike are creeping into its backyard with similar AI-driven services. SentinelOne still has a lot to prove, but it could surprise investors over the next few years as it scales up its business. That expansion and evolution would likely drive its stock much higher. Leo Sun has positions in CrowdStrike. The Motley Fool has positions in and recommends CrowdStrike and Zscaler. The Motley Fool has a disclosure policy. With the Addition of New Passwordless Authentication Options, CyberArk Furthers Its Commitment to Helping Customers Reduce Credential Theft and Strengthen Productivity CyberArk (NASDAQ: CYBR), the identity security company, today announced it has expanded passwordless authentication capabilities with new passkeys support. Now, CyberArk Identity customers can accelerate passwordless adoption and reduce cybersecurity risk by enabling the use of passkeys to easily access apps and websites using strong authentication methods like biometrics. Stealing or abusing credentials to compromise identities is how most breaches begin. Passkeys extend a passwordless strategy to reduce the attack surface and minimize credential theft. The addition of passkeys provides CyberArk Identity customers with phishing-resistant, FIDO2-compliant credentials that replace passwords, providing the strongest level of protection against identity theft and account takeover and is a NIST Authentical Assurance Level (AAL3) authentication method. Additionally, passkeys work across user devices, and even work on those within physical proximity, improving user experiences by simplifying and speeding up authentication flows. CyberArk Identity delivers a set of SaaS solutions designed to simplify enterprise identity and access management while providing a high level of security. Part of the CyberArk Identity Security Platform, CyberArk Identity helps today’s businesses overcome user authentication, authorization and identity management challenges accompanying business transformation initiatives. With the CyberArk platform, organizations can enable Zero Trust and least privilege with complete visibility, enabling every identity to access any resource more securely, located anywhere, from everywhere – and with intelligent privilege controls. CyberArk Identity also provides support for YubiKey One Time Passcode (OTP). YubiKey is a widely used physical authentication device that complies with NIST 800-63B guidelines regarding Authentication Assurance Level 2 (AAL2). With the OTP generated by their YubiKey, users can securely authenticate to any application protected by CyberArk Identity. “Passwords are the weakest link in the security chain, and they are often the root cause of data breaches and cyberattacks. By introducing passkeys for passwordless authentication, we are further enabling our customers to eliminate passwords from their authentication workflows,” said Gil Rapaport, general manager, Access, CyberArk. “CyberArk is committed to delivering the most comprehensive and innovative identity security solutions on the market. By extending passwordless authentication options, not only are we helping to eliminate password-based risk for our customers, but we are also improving productivity and the overall user experience.” CyberArk was named an Overall Leader in the KuppingerCole Analysts AG “Leadership Compass: Passwordless Authentication”1 report. CyberArk was highlighted as a “comprehensive, feature-rich and modern passwordless solution.” According to the report, CyberArk Identity stood out for advantages such as providing a solution for securing remote access and BYOD scenarios, flexible deployments, integration with CyberArk privileged access management solutions, strong partner ecosystem and proven scalability. Passwordless authentication with passkeys is available now as part of the CyberArk Identity 23.11 release. Additional Resources
About CyberArk CyberArk (NASDAQ: CYBR) is the global leader in identity security. Centered on intelligent privilege controls, CyberArk provides the most comprehensive security offering for any identity – human or machine – across business applications, distributed workforces, hybrid cloud environments and throughout the DevOps lifecycle. The world’s leading organizations trust CyberArk to help secure their most critical assets. To learn more about CyberArk, visit https://www.cyberark.com, read the CyberArk blogs or follow on LinkedIn, X, Facebook or YouTube. View source version on businesswire.com: https://www.businesswire.com/news/home/20231121808245/en/ CyberArk Elevates Passwordless Experience with New Passkeys Authentication With the Addition of New Passwordless Authentication Options, CyberArk Furthers Its Commitment to Helping Customers Reduce Credential Theft and Strengthen Productivity CyberArk (NASDAQ: CYBR), the identity security company, today announced it has expanded passwordless authentication capabilities with new passkeys support. Now, CyberArk Identity customers can accelerate passwordless adoption and reduce cybersecurity risk by enabling the use of passkeys to easily access apps and websites using strong authentication methods like biometrics. Stealing or abusing credentials to compromise identities is how most breaches begin. Passkeys extend a passwordless strategy to reduce the attack surface and minimize credential theft. The addition of passkeys provides CyberArk Identity customers with phishing-resistant, FIDO2-compliant credentials that replace passwords, providing the strongest level of protection against identity theft and account takeover and is a NIST Authentical Assurance Level (AAL3) authentication method. Additionally, passkeys work across user devices, and even work on those within physical proximity, improving user experiences by simplifying and speeding up authentication flows. CyberArk Identity delivers a set of SaaS solutions designed to simplify enterprise identity and access management while providing a high level of security. Part of the CyberArk Identity Security Platform, CyberArk Identity helps today’s businesses overcome user authentication, authorization and identity management challenges accompanying business transformation initiatives. With the CyberArk platform, organizations can enable Zero Trust and least privilege with complete visibility, enabling every identity to access any resource more securely, located anywhere, from everywhere – and with intelligent privilege controls. CyberArk Identity also provides support for YubiKey One Time Passcode (OTP). YubiKey is a widely used physical authentication device that complies with NIST 800-63B guidelines regarding Authentication Assurance Level 2 (AAL2). With the OTP generated by their YubiKey, users can securely authenticate to any application protected by CyberArk Identity. “Passwords are the weakest link in the security chain, and they are often the root cause of data breaches and cyberattacks. By introducing passkeys for passwordless authentication, we are further enabling our customers to eliminate passwords from their authentication workflows,” said Gil Rapaport, general manager, Access, CyberArk. “CyberArk is committed to delivering the most comprehensive and innovative identity security solutions on the market. By extending passwordless authentication options, not only are we helping to eliminate password-based risk for our customers, but we are also improving productivity and the overall user experience.” CyberArk was named an Overall Leader in the KuppingerCole Analysts AG “Leadership Compass: Passwordless Authentication”1 report. CyberArk was highlighted as a “comprehensive, feature-rich and modern passwordless solution.” According to the report, CyberArk Identity stood out for advantages such as providing a solution for securing remote access and BYOD scenarios, flexible deployments, integration with CyberArk privileged access management solutions, strong partner ecosystem and proven scalability. Passwordless authentication with passkeys is available now as part of the CyberArk Identity 23.11 release. Additional Resources
About CyberArk CyberArk (NASDAQ: CYBR) is the global leader in identity security. Centered on intelligent privilege controls, CyberArk provides the most comprehensive security offering for any identity – human or machine – across business applications, distributed workforces, hybrid cloud environments and throughout the DevOps lifecycle. The world’s leading organizations trust CyberArk to help secure their most critical assets. To learn more about CyberArk, visit https://www.cyberark.com, read the CyberArk blogs or follow on LinkedIn, X, Facebook or YouTube. View source version on businesswire.com: https://www.businesswire.com/news/home/20231121808245/en/ | ||||||||
CAU302 study help | CAU302 health | CAU302 Questions and Answers | CAU302 exam Questions | CAU302 Free PDF | CAU302 exam Questions | CAU302 exam syllabus | CAU302 course outline | CAU302 certification | CAU302 questions | | ||||||||
Killexams exam Simulator Killexams Questions and Answers Killexams Exams List Search Exams |